Inside the Scammer’s Mind: Attack Data Revealed
Inside the Mind of a Scammer: New Research That Unravels the Latest Fraud Trends
To outsmart cybercriminals, you need to get inside their heads—decipher their motives, anticipate their tactics. That’s exactly what our team of experts at Arkose Labs did. We pored over 12 months of data from some of the most heavily targeted businesses across industries, uncovering fascinating and alarming trends that every enterprise should know about.
Our hot-off-the-presses report, A Data-Driven Analysis of Threat Actor Behavior, explores the scammer psyche in depth. The findings are a must-read for any executive serious about protecting their consumers and their bottom line. Let’s dive into three key insights that I found particularly illuminating.
Account Sign-up: Still the Scammer’s Favorite
First up, account sign-up remains the most popular attack vector for scammers. Threat actor group Storm-1152 created 750 million fake Microsoft accounts and made millions of dollars selling them on the dark web. It’s not hard to see why, right? Targeting the registration process offers fraudsters the best bang for their buck—low effort, high reward. By slipping past defenses here, they can establish a foothold and launch future attacks with ease.
But here’s the thing: these crooks are as clever as they are lazy. They’ll abuse the anonymity of account creation to scale up their scams, creating hordes of fake users to amplify their profits. The lesson? Lock down your sign-up flow like your business depends on it—because in many ways, it does.
Sign-up isn’t the only vulnerability, of course. Our analysis shows how scammers are targeting other critical touchpoints like account sign-in and password resets. Curious to see the other key customer touchpoints scammers are targeting? You can get access to the full view of these attack points in the report.
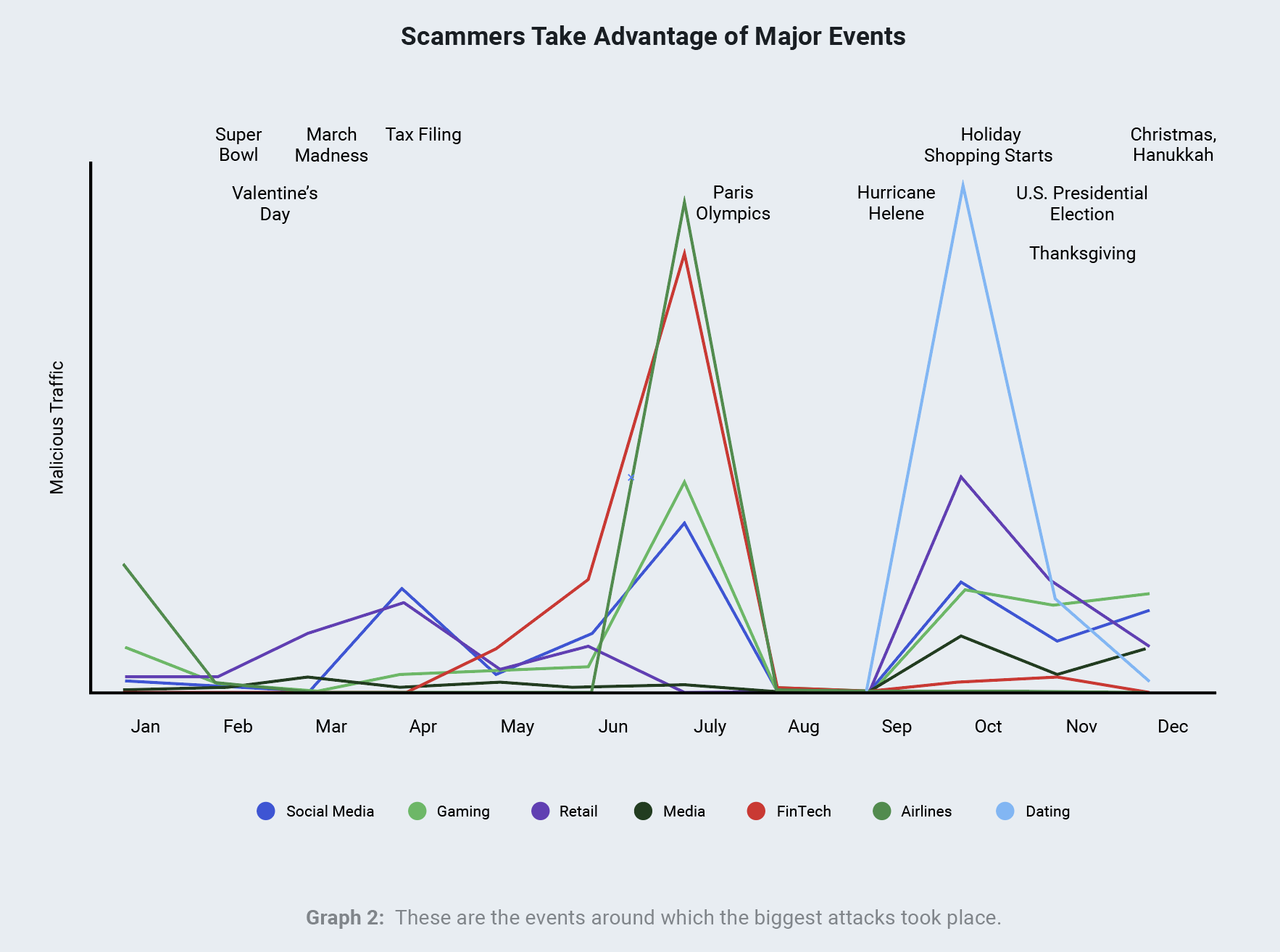
Scammers’ Seasonal Strategy: A Year-Long View
Now, let’s step back and look at attack patterns over an entire year. One striking theme emerges—these aren’t random hits, but carefully timed campaigns designed by scammers to maximize impact.
Take the travel industry. During peak vacation booking seasons, our data shows a significant spike in attacks targeting online travel agencies and airlines. Meanwhile, in the world of online gaming, fraudsters lie in wait for major game launches or in-game promotions, then flood gaming platforms with fake sign-ups to snag valuable bonuses.
The takeaway? Stay vigilant during “slow” periods, and ramp up defenses ahead of high-risk moments. Anticipating scammers’ timing is half the battle.
The 9-to-5 Fraudster: Not Just a Hobby Anymore
So who are the criminals behind these attacks? Just bored basement-dwellers, sophisticated Nation State actors, or professional con artists? A little bit of all of them but our research points to the latter, but with some side-hustle sprinkled in.
When we analyzed attack patterns across global time zones, we noticed something fascinating. In certain regions, fraudsters operated in surprisingly consistent “business hours,” attacking in regular 9-to-5 patterns. What does this mean? For many, fraud is now a full-time job. In Mexico, for example, the majority of attacks originate during standard workday hours, then trail off in the evening—a classic “shift work” pattern.
And it makes sense when you look at how much scammers can earn compared to the average annual salary for a software developer. Take El Salvador, where fraudsters might make 20x more attacking gaming companies versus working a software developer job.
Download the full report for an eye-opening breakdown of fraudsters’ “business models” in key countries. Fair warning: it’s a glimpse into the professional fraud economy that may challenge some of your assumptions.
Knowledge is Power: Arm Yourself with Insights
There’s a wealth of insights packed into our new analysis. This resource is your guide to the criminal mind, filled with information you can use to stay multiple steps ahead of even the craftiest fraudsters.
In this cat-and-mouse game, the prepared player prevails. As I see it, the key to winning this battle is threefold:
- Prioritize hardening your most valuable and vulnerable workflows, focusing on the human element (remember the adversaries are exceptional students of human psychology).
- Break down internal data silos—share threat intel across teams to stay one step ahead.
- Train, train, train. Educate your team to spot and stop scams instinctively.
Want to dive deeper into these insights? Download the full report for comprehensive data, industry-specific analysis, and actionable defense strategies. And if you’re staring down an urgent situation or have questions? Just reach out to me directly!