Your SMS Verification Flow Is a Revenue Stream for Fraud Farms

Most fraud teams think about SMS fraud as a cost problem. A spike in OTP sends, an unexplained jump in carrier charges, a line item in the communications budget that doesn’t track to growth. The assumption is that something went wrong operationally.
The reality is more deliberate. SMS toll fraud, also known as artificially inflated traffic or AIT, is not a billing anomaly. It is a revenue model. And human fraud farms are the mechanism that makes it work at scale.
How SMS Toll Fraud Actually Works
The mechanics are straightforward. Attackers register phone numbers connected to premium-rate lines that generate carrier payouts for every message received. They then need a way to trigger large volumes of SMS sends from a legitimate platform toward those numbers. The trigger is almost always an ordinary authentication flow: account registration, OTP delivery, password reset, phone number verification.
Every message the platform sends to an attacker-controlled number is a transaction. The platform pays the carrier. The carrier pays out to the premium-rate line. The attacker collects the margin. The platform absorbs the cost with no fraudulent transaction ever completed in the conventional sense, no account taken over, no payment stolen. The infrastructure itself is the product being exploited.
A single campaign can generate hundreds of thousands of SMS sends before the cost anomaly surfaces in reporting. By then, the operation has typically moved on.
Where Human Fraud Farms Enter the Picture
The bottleneck for any SMS toll fraud operation is the authentication flow. Platforms have spent years adding bot detection, rate limiting and challenge-response tests to SMS-triggering endpoints precisely because the exposure is high and the abuse surface is obvious. Automated tools hit those defenses and stop.
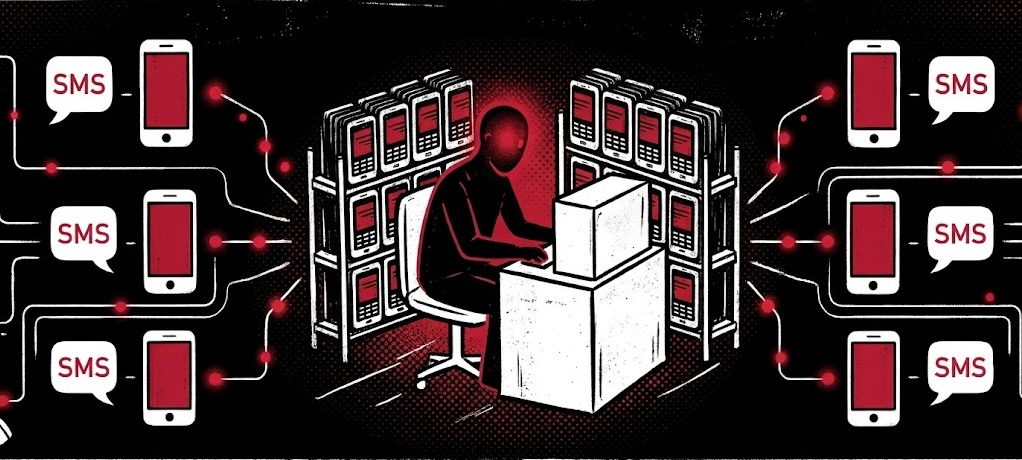
Human fraud farms exist specifically to go where automation cannot.
These are organized networks powered by coerced labor or work-from-home employees in low-wage areas, often recruited through social media and messaging platforms under the pretense of legitimate remote data entry work, and paid per task completed. Workers generate authentic behavioral signals: real mouse movement, natural typing cadence, genuine dwell time on page. They solve challenge-response tests designed to filter machines, because they are not machines. They use residential proxy addresses that pass reputation checks. And they operate at low enough volume per worker to stay below the velocity thresholds that would trigger an alert.
The individual session is indistinguishable from a legitimate consumer. That is not a flaw in the operation. It is the design.
A single human fraud farm operation can deploy dozens to hundreds of workers simultaneously, each completing registration flows and triggering SMS sends toward premium-rate numbers. At scale, this produces the volume required to make the toll fraud economics work, with no signal that automated detection was built to catch.
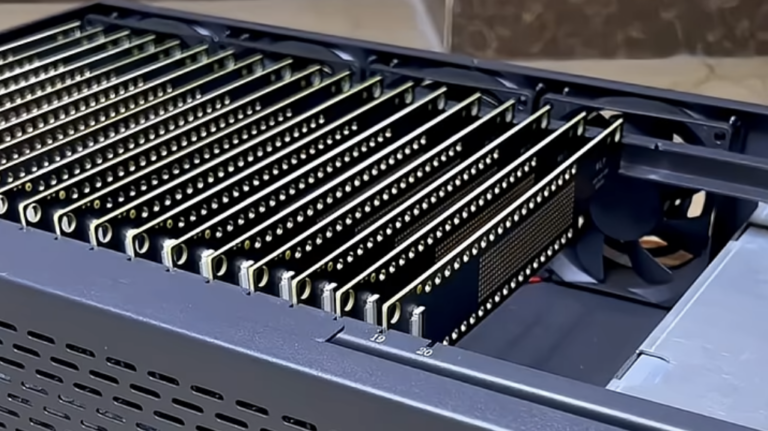
The Arkose Labs ACTIR unit has also observed hybrid variants where human fraud farm operations coordinate alongside mobile device farms — a distinct infrastructure layer in which attackers deploy banks of physical devices to generate device fingerprints and complete verification flows at scale, blending into legitimate mobile traffic patterns. These are separate attack categories, but they increasingly operate in coordination: human workers handle the steps requiring genuine interaction while mobile device farm infrastructure provides additional evasion coverage. The result is a compounding attack against which standard defenses have no adequate response.
Why the Detection Stack Misses It
The standard fraud detection model is built to answer one question: is this session suspicious? For SMS toll fraud executed through human fraud farms, the session-level answer is almost always no.
Workers on real devices generate the behavioral signals that behavioral analytics score as legitimate. Standard challenge-response tests confirm them as human. Residential IPs pass reputation checks. Session volume per worker stays below velocity thresholds.
There is no individual signal to catch. The fraud is visible only at the pattern level, across sessions, devices, accounts and time, where the coordination of a managed operation becomes apparent. That kind of cross-session, cross-flow intelligence is exactly what point solutions and single-flow detection tools do not have.
There is also a timing problem that makes detection-first approaches structurally inadequate for this threat. SMS toll fraud accrues cost before any conventional fraud signal appears. No account is taken over. No payment is disputed. No chargeback is filed. By the time the cost anomaly surfaces in reporting, the operation has run its campaign and moved to the next target. Detecting what happened is possible. Preventing the cost from accumulating requires intercepting the session before the SMS trigger fires, not after.
The Economic Structure of the Attack
Human fraud farm operations are businesses. They have labor costs, tooling overhead, coordination expenses and margin requirements. Workers are paid per task completed. Coordinators monitor defensive responses and adjust tactics. Operators make deliberate ROI decisions about which platforms to target, which flows to hit, and when to scale up or down based on defensive countermeasures.
For SMS toll fraud specifically, the revenue model creates a direct and measurable attacker incentive. A campaign that triggers 500,000 SMS sends at an average carrier cost of a few cents per message generates significant attacker revenue while costing the platform the same amount in communications budget. The operation does not need to steal anything. It needs only to trigger sends.
This is why detection-first approaches fail structurally against this threat. Blocking a session costs the attacker nothing. Workers rotate proxies, adjust browser profiles, and retry. The cost of retrying is near zero. Meanwhile, the platform has already absorbed the cost of every send that completed before the block. The economics favor the attacker until the platform changes the model entirely, from one that reacts to sessions that look suspicious to one that imposes cost on every suspicious attempt before it completes.
What the Defense Looks Like
Stopping SMS toll fraud through human fraud farms requires intercepting sessions at the flow entry point, before the SMS trigger fires. That means detection and enforcement upstream of the action, not downstream of the cost.
The Arkose Labs economic deterrence model is built for exactly this architecture. Challenge enforcement at the registration and verification flow entry point stops sessions before they reach the trigger. For human fraud farm-flagged traffic, challenges escalate in difficulty and duration, requiring genuine cognitive effort and taking significantly longer to complete than the standard worker workflow allows. Proof-of-Work computation layers add a silent compute cost that accumulates across a large workforce. Combined, these mechanisms raise the per-session cost for farm operators until the campaign stops generating positive returns.
Field intelligence from attacker-facing solver marketplaces confirms that this works in practice. On platforms where fraud farm workers source challenge-solving labor, Arkose Labs challenges are consistently the most expensive to solve, priced at up to roughly $50 per 1,000 solves compared to $1 to $3 for standard alternatives. Workers on these platforms describe Arkose Labs challenges as too slow, too difficult and not worth completing at their pay rate. That is attacker-sourced evidence that the economics are working.
Persistent device identification compounds the deterrence. When device history follows workers across proxy rotations and browser profile resets, the cost of each new attempt increases. Workers cannot effectively reset and retry at the low cost that makes high-volume campaigns viable.
Arkose Labs Email Intelligence addresses the identity layer at registration. Flagging disposable, bulk-generated and breach-associated addresses before accounts are created forces operators to invest in higher-quality identity material, raising the per-account cost of building the attack inventory before any challenge is served.
For hybrid operations involving mobile device farms, Arkose Labs Device ID identifies the device fingerprint patterns that distinguish farm infrastructure from legitimate mobile traffic, extending deterrence to that parallel evasion layer.
A Note on the AI Evolution
The human fraud farm threat does not stand still, and SMS toll fraud is no exception to its evolution.
AI agents are being layered into fraud farm operations to handle coordination, real-time adaptation and, increasingly, the execution layer itself. For SMS toll fraud, this means AI-assisted operations can probe SMS-triggering endpoints session by session, identify gaps in detection, and shift tactics mid-campaign without human intervention and without the psychological friction that makes sustained challenge completion difficult for human workers.
AI agents do not get frustrated. They do not quit because the work is too slow or the pay is not worth the effort. The deterrence model has to account for this.
The Arkose Labs agentic AI classification capability classifies traffic as human, traditional bot or AI agent, and applies policy responses appropriate to each threat type. Challenge technology includes types specifically designed to impose cost on AI solvers, not just human workers. Economic deterrence applies to AI-augmented operations by the same logic it applies to human ones: when every attempt costs compute, every challenge consumes time, and every identity requires real investment to generate and maintain, the ROI of the campaign deteriorates. When the cost of the attack exceeds the expected return, the operation stops, regardless of whether it is run by a room of workers, an AI agent, or a combination of both.
What to Do With This Information
If your platform uses SMS for any part of the authentication or verification flow, the exposure is real and the attack pattern is active. The questions worth asking are direct ones.
Has your SMS spend increased without a corresponding increase in legitimate account creation or verification? Are your existing bot detection and challenge-response tools deployed on the specific flows that trigger SMS sends, or only on downstream payment and transaction flows? Can your fraud team see cross-session patterns across registration and verification, or only session-level signals at individual endpoints?
The gap between where bot detection is deployed and where SMS triggers fire is where this attack lives. Closing it requires enforcing economic deterrence at the entry point, before the trigger fires and before the cost accrues.
Arkose Labs protects platforms from SMS toll fraud, human fraud farms and AI-augmented hybrid attacks through economic deterrence applied at every suspicious session. Learn how to stop fraud before it costs you with the Arkose Titan platform.