The Pros and Cons of reCAPTCHA Enterprise
Google’s web security service, reCAPTCHA, is seemingly ubiquitous on the internet. Virtually anyone who has logged into one digital account or another has encountered this authentication service and clicked on more pictures of buses and traffic lights than they’d care to think about.
One reason for reCAPTCHA’s initial widespread use was that it was free. Any company doing business online that wants a modicum of bot protection could integrate it on login or registration pages without investing a dime.
But then Google released reCAPTCHA Enterprise, which charges its users based on monthly usage. The enterprise version is free for up to 1 million assessments per month, but larger companies could easily surpass those limits. That has businesses asking themselves:
“Is it worth it for our organization to invest in reCAPTCHA Enterprise?”
The answer depends on many factors, including a company’s security requirements and the tool’s overall cost. Here’s a look at what reCAPTCHA Enterprise offers, its pros and cons, and how it fits into the CAPTCHA marketplace.
How reCAPTCHA Enterprise works for bot detection
According to its own description, Google uses “an advanced risk analysis engine” to determine the suspicion level of traffic to a website. Any traffic that is deemed suspicious is served a reCAPTCHA enforcement challenge. This can entail either only clicking the “I’m not a robot” box, or also picking out mundane everyday items from a grid.
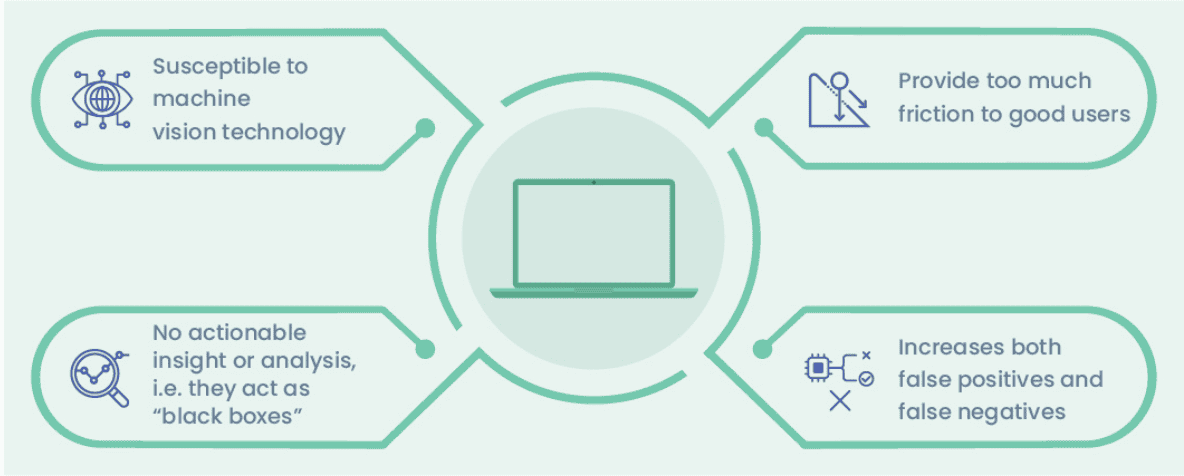
A few common issues arise with this approach.
Good users are often classified as suspicious
Google’s “advanced risk analysis” noted above is heavily dependent on the use of Google cookies1. That means if you are a Chrome user, or are logged into a Google account such as Gmail, Google knows much more about you and how “suspicious” your web activity is. So users of Google products and services will likely bypass any reCAPTCHA challenge.
Bots have become adept at solving puzzles
Image recognition software has gotten so advanced that it can easily solve most reCAPTCHAs with little difficulty2. And it’s easy to get a hold of software to do just that. A simple web search for bots that solve reCAPTCHA turns up dozens of results, some of which offer access to automated scripts for as little as $20/year. An American computer science professor used off-the-shelf image recognition tools to solve Google’s image CAPTCHAs with 70 percent accuracy.3
Even AI tools have gotten in on the game, as earlier this year a ChatGPT tricked a human into helping it bypass a CAPTCHA test.4
reCAPTCHA Limitations
What is the difference between reCAPTCHA and reCAPTCHA Enterprise?
In response to many of these concerns, Google rolled out v3 of its security solution, followed by the Enterprise version, which was built on everything v3. So how exactly is this latest version different from earlier iterations?
The biggest change is that it aims to show far fewer challenges to the user. Instead, reCAPTCHA Enterprise works “invisibly” in the background, constantly monitoring user behavior to determine whether each visit to a site is a human or a bot.
Google then returns a risk score to website administrators between 0 and 1. 0 means you’re definitely a bot, 1 means you’re definitely a human, and in between is a very large gray area. Website admins then must decide what to do based on the score they receive for each user.
reCAPTCHA Enterprise still favors users of Google products
Much like its predecessors, newer versions of reCAPTCHA still largely look at whether you have Google cookies on your browser to determine if you are suspicious. According to a Fast Company article, “With reCAPTCHA v3, technology consultant Marcos Perona and Mohamed Akrout’s tests both found that their reCaptcha scores were always low risk when they visited a test website on a browser where they were already logged into a Google account.” 5
Therefore, those using browsers other than Chrome or tools to maintain online privacy will likely face friction.
Furthermore, it should be noted that any environment that doesn’t enable cookies will automatically lead to much higher instances of good users seeing reCAPTCHA challenges. This includes when authenticating on iOS and Android apps, as well as desktop applications such as launching apps for PC video games.
This is also an issue for users in places where Google does not have a presence. Take mainland China, where Google is banned. It’s one of the largest economies and consumer markets in the globe. No Google means no Google cookies, so users almost always have to solve challenges. It’s plainly apparent that a cookies-based approach to authentication is not viable in the long term.
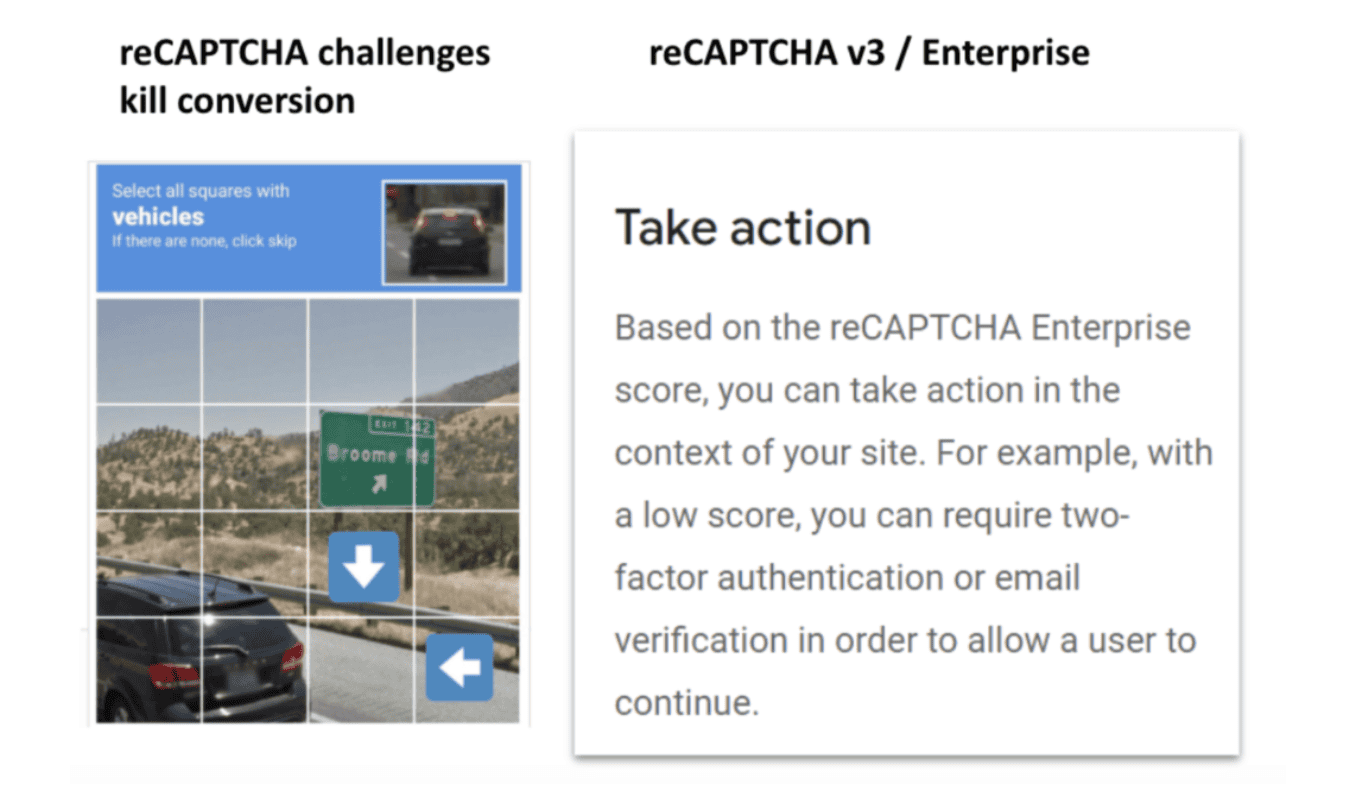
reCAPTCHA is still the same challenge
So, what do you do for your users who get assigned high-risk scores? Well, you have a few options. One is to serve them a challenge…which is exactly the same reCAPTCHA it has always been. Any business deploying reCAPTCHA Enterprise is still going to have only the same old reCAPTCHA grid with picking crosswalks available to them if they want to serve a challenge to suspected suspicious traffic. Website operators can also choose to trigger two-factor authentication (2FA) for those with low scores, but this provides even more friction to potential good users than solving a CAPTCHA.
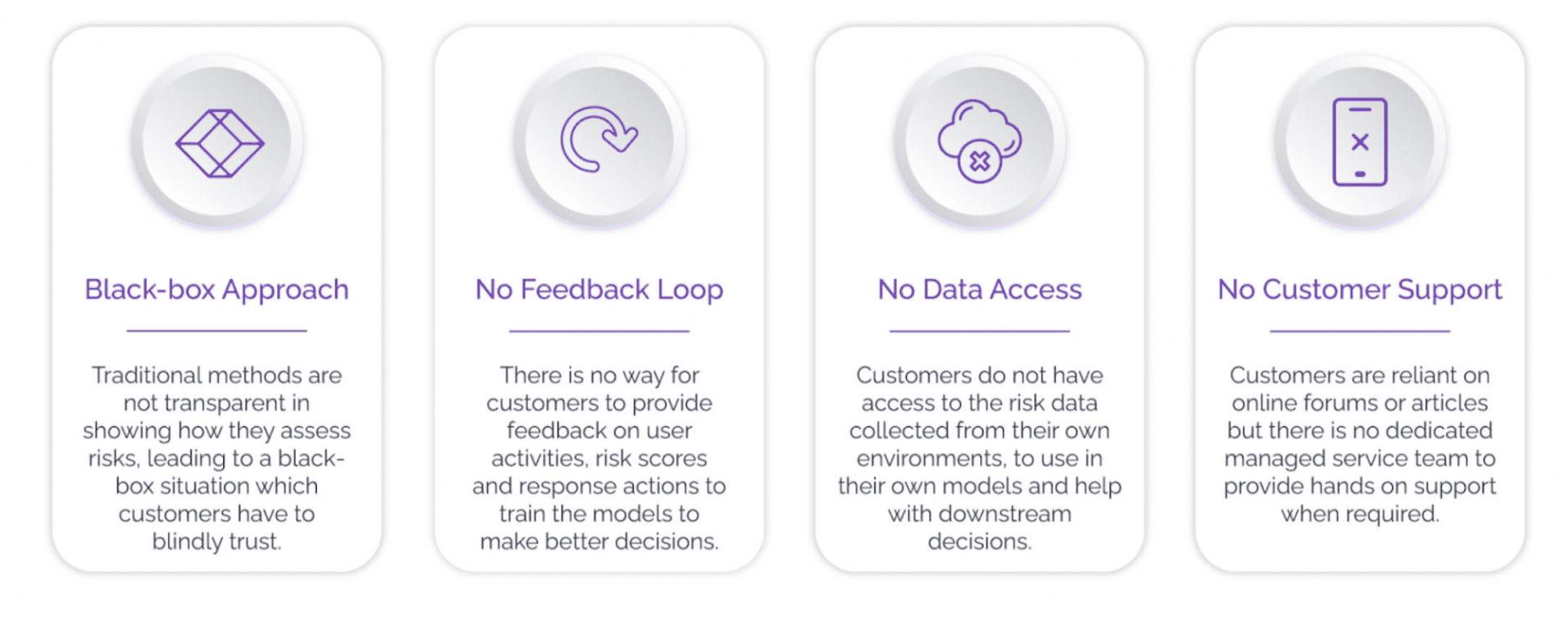
A “Black Box” with No Data
The main issue with a risk scoring system is one that has long been an issue for users of reCAPTCHA or many other services: There is no insight or data analytics.
Google can tell you if it thinks someone is suspicious, but not what to do about it. If you are a website admin, at what score do you draw the line for challenging a user? Is it .15? .25? Ultimately, any web pages using reCAPTCHA will end up either blocking too many good users or being too lax and letting too many attackers through.
Businesses need insight into attack patterns to be able to stop future threats. Without a constant feedback loop refining the accuracy of its risk scores, reCAPTCHA or another CAPTCHA solution cannot learn or evolve to defend against the ever-changing threat landscape.
Which CAPTCHA should I use?
When choosing the best CAPTCHA solution, businesses need more than just a tool that stops bots. They need a solution that adapts to the ever-changing landscape of bot attacks while preserving a seamless experience for legitimate users. This is where Arkose Labs stands apart.
Unlike reCAPTCHA Enterprise, which still relies on Google’s cookie-based risk scoring and leaves many businesses in the dark with insufficient data, Arkose Labs provides a comprehensive, adaptive approach to bot prevention. Through real-time digital risk intelligence, Arkose Labs analyzes risk signals from a variety of sources, including device information, email behavior, and even phishing intelligence. This allows businesses to not only prevent bots but also make informed decisions about security in real time.
What makes Arkose Labs truly unique is its ability to stop sophisticated bots while enhancing the user experience. In the Arkose MatchKey component of the Arkose Labs solution, we use AI-resistant challenges that are constantly evolving to keep up with the latest in machine learning and AI-based bot technology. These challenges don’t just confuse bots; they engage legitimate users, turning security into a positive experience rather than a frustrating hurdle.
Furthermore, Arkose Labs goes beyond just providing a CAPTCHA. Our solutions offer deep insights into attack patterns and ongoing fraud trends, thanks to our vast intelligence network. This allows businesses to stay ahead of the curve, proactively mitigate emerging threats, and ultimately reduce both the cost and impact of fraud.
For organizations seeking a solution that goes beyond CAPTCHA, Arkose Labs offers the technology, expertise, and global threat intelligence necessary to protect against today’s most advanced cyberattacks, ensuring that your business can continue to thrive securely.
Learn more about how we can help or book a demo.