As the holiday season ramps up, online gamers spend more time in their favorite virtual worlds. From Nintendo to Xbox to "God of War" and "Call of Duty," a flood of video games appear on the scene, encouraging players to invest even more time and money in this form of competitive entertainment.
There are an estimated 3 billion gamers around the world, which translates to a growing attack surface for digital fraudsters. While players are focused on racking up points and bonuses, bad actors are watching from the sidelines, ready to make moves of their own.
The holiday season is also a time when gaming companies sweeten the pot for players, often making big announcements and promoting new in-game releases. This all adds up to more platform engagement for gamers, and fraudsters will leverage this boom. It also means gaming companies are positioned to see sophisticated new attack strategies. So, how can they adapt quickly and keep their platforms safe?
Gaming Attacks
Online fraudsters understand the potential. The gaming sector hosts a large community of young users, many of whom have never been swept up in a data breach. Bad actors take advantage of this demographic by targeting high-value accounts to gain items they can resell in the real world—and for real money. During an account takeover, a player’s entire balance can be transferred into an attacker's account. Once this happens, the attacker can cash out using services that turn gaming currency into real dollars. Compared to other industries, the gaming industry has a lot of money-making potential for skilled attackers with good reputations.
Fraudsters will register for multiple new accounts with bonus offers and create fake gaming sessions for financial gain. According to Brett Johnson, Chief Criminal Officer at Arkose Labs, “There are four things cybercriminals are looking for: information, access, data, and cash.” Promotions in gaming may attract new customers, but fraudsters are looking to take advantage of them and make money by making multiple accounts with fake names.
Johnson also points out that as macroeconomic conditions decline, cybercrime goes up, which is why cybercrime-as-a-service (CaaS) is on the rise. In addition to the familiar attacks like credential theft, attack trends also indicate a new focus on stealing session tokens, or cookies. CaaS provides automated ways for new, unskilled attackers to enter markets without building their own malicious bots from scratch.
To learn more about cybercrime in the online gaming industry, download the Q4 Report: Gaming Industry Threats Leveling Up: Fraud Farms and Bot Attacks Among Leading Dangers.
Threat Landscape for Gamers
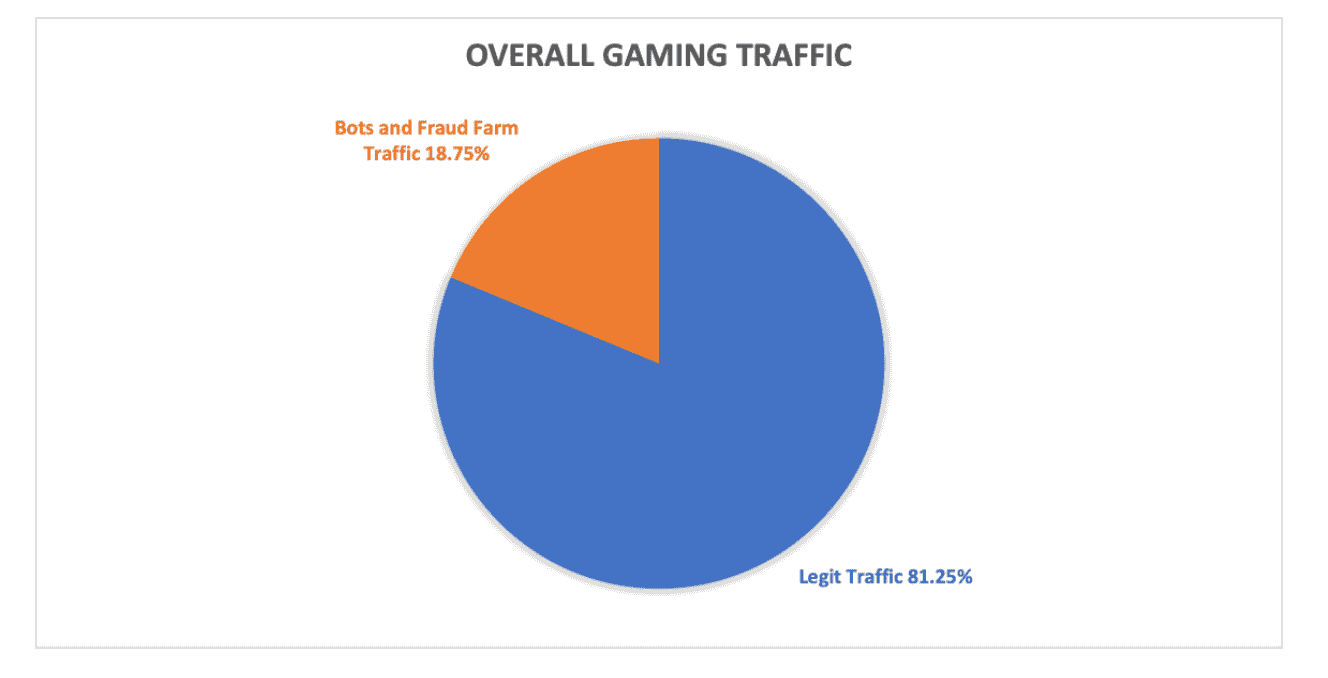
In Gaming Industry Threats Leveling Up: Fraud Farms and Bot Attacks Among Leading Dangers, Arkose Labs analyzed close to 8 billion sessions from the world’s largest gaming businesses and discovered the four main areas of traffic include:
- Malicious bots
- Intelligent bots
- Fraud (click) farms
- Legitimate users
During the holiday season, both gamers and online gaming companies are targeted by basic and intelligent bots at the point of registration, although fraud farms remain a static threat. Registration attacks are, in fact, the most common type of threat. In fact, attackers sign up for dozens of domains so that WAF-deny lists and spam filters won't notice them.
These attacks often focus on new account registration because it offers a blank slate for fraud. After registering for new accounts, bad actors actually play / hack the game to raise the expertise and benefits of the player profile, making it highly attractive to those in the gaming chair. But once the real gamer buys the well-stocked account, the site sees the fraud and shuts down the account. This means the fraudsters win, players lose. As with basic and intelligent bots, fake account registration and theft of login credentials remain the most common types of fraud.
New Gaming Threats on the Horizon
Fraudsters are constantly innovating and shapeshifting. Some of the most recent attack trends in the gaming sector include:
Reverse proxy phishing
Also known as Man-in-the-Middle (MITM) attacks, this threat is among the fastest growing type of internet crime. This is a general term for when a bad actor intercedes between a user and an application, either to listen in or even impersonate one side, making it seem as if all is normal.
Volumetric DDoS attacks
Launched by both basic and intelligent bots, this attack attempts to collapse servers without affecting users, typically on login and signup pages. Look for unusually large traffic visible to target and upstream connectivity providers.
Discord for Communications
Most gamers use Discord, a VoIP and instant messaging platform, for legitimate purposes; however, it is also a meeting place for fraudsters looking to send malware and remote-access trojans.
Find more detailed information on these attacks in our newest Q4 Report: Gaming Industry Threats Leveling Up.
Hard Lessons in Gaming
The recent uptick in gaming threats demonstrates how cybercriminals can use automated, bot-based attacks in other verticals. “Pay attention to the gaming industry,” Johnson says. “It is the testing ground for most automated types of attacks.” Criminals look for ways to automate the types of fraud that humans are committing in other industries. “Once those automated ways are proven effective in that testing ground, then they’ll start deploying them in other verticals,” Johnson says.
Arkose Labs Protects Online Gaming Companies
At Arkose Labs, we make attacks more difficult and costly for fraudsters, dismantling their economic incentive by challenging them to clear enforcement tests at scale. To complete the attack, fraudsters must spend more time and invest in additional resources and machine learning.
We protect global gaming companies from constantly changing attacks, stop automated activities that try to make money off of stolen data, and stop match-fixing in games. Our unique detection and mitigation platform looks at data from user sessions to figure out the context, behavior, and reputation of every request. We classify traffic based on its risk profile and present suspicious traffic with enforcement challenges to differentiate between true users and fraudsters.
To learn more, read our Q4 Report on gaming or contact us for more information.


