WHY CHOOSE ARKOSE LABS
Secure trust from the start. Stop fraud before impact.
When security is paramount, top gig economy platforms turn to Arkose Labs.
225+ signals and assessments shared
Intelligence to enrich and tune your decisioning.
Financial Warranties
Best efforts aren’t good enough. We back our platform with million-dollar warranties and SLAs.
Arkose Global Intelligence Network
We see 90% of internet traffic every 20 minutes. Benefit from global risk signals and mitigation intel from our customer base.
Trusted by the most recognizable brands in the world
Built for enterprises, our technology, support, certifications and architecture meet your scalability requirements.
Global, proactive support
24/7/365 real-time SOC support with proactive incident response vs. “on call”.
Harnessing AI to stop evolving threat vectors
We’re leveraging AI to defend against AI-driven bots.
AWARD-WINNING EXCELLENCE
Celebrating our commitment to innovation, customer satisfaction and growth.
RECOMMENDED RESOURCES
Better understand cyber threats in sharing economy.

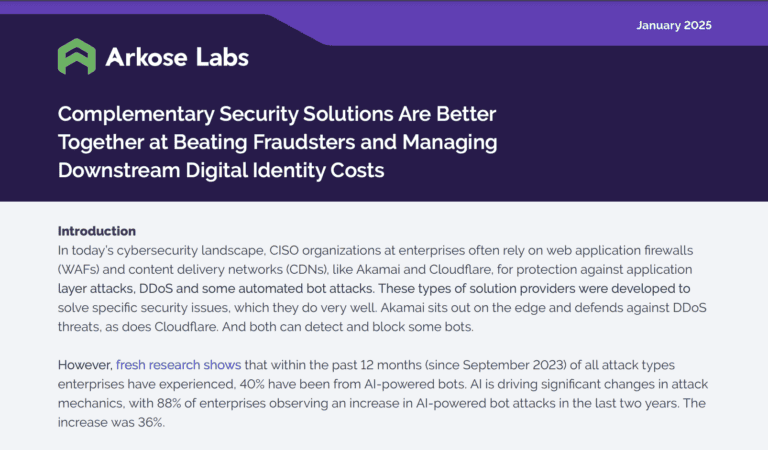
Better Together: Arkose Labs, CDNs & WAFs