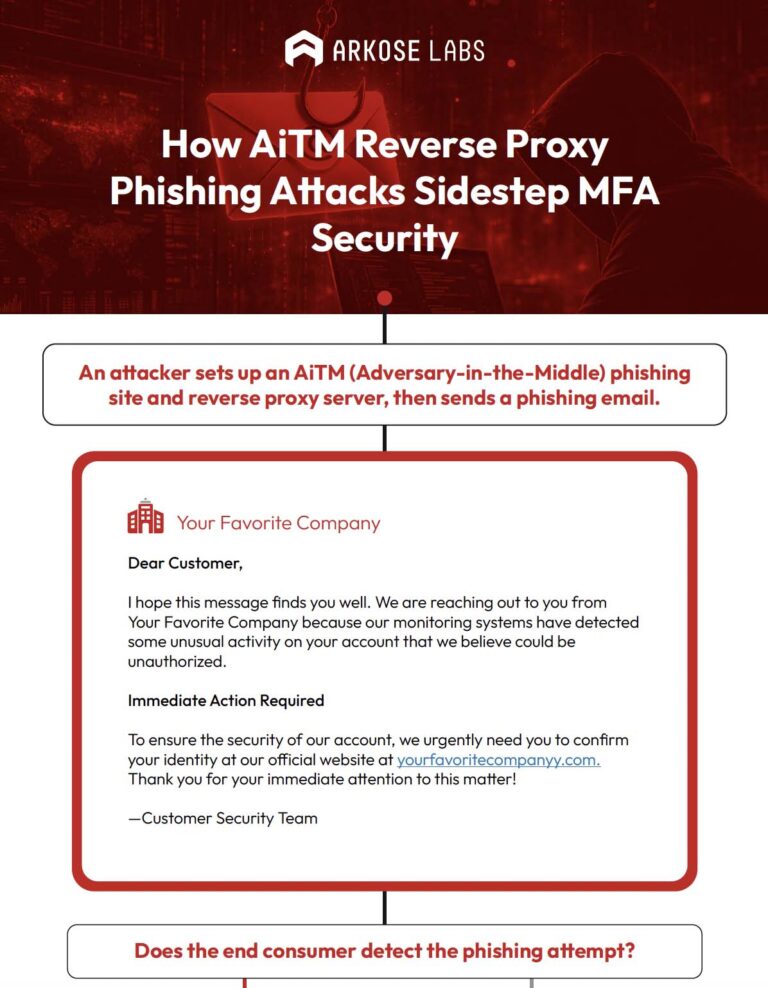
Because getting past MFA protections is easier than you think.
Safeguard your consumers in real time from falling prey to reverse-proxy sites that mimic legitimate ones. Proactive detection from Arkose Labs protects against the misuse of intercepted credentials and multi-factor authentication codes.