What is device intelligence?
The always-on, smart devices are making it easier for consumers to complete a wide variety of life activities digitally. However, billions of connected devices make it difficult for businesses to strike a balance between fraud prevention and seamless user experience. Accurately identifying spoofed devices from genuine consumers, without disrupting user experience is a challenge that digital businesses are continuously facing.
Device intelligence is a process of collecting device information, analysis and identity validation to allow business to accurately ascertain who is on the other side of the device. It plays a key role in protecting businesses and their customers from a number of cyber threats. Cloud-based device intelligence solutions collect hundreds of data points related to the device, analyze them using advanced machine learning models, and accurately distinguish between genuine and rogue devices in real-time for superior fraud prevention.
What is device intelligence used for?
Bad actors often use stolen consumer information for spoofing or changing the settings of browsers or devices to impersonate genuine users. Device intelligence uses digital device forensics to identify anomalous user activity, such as using the same device for multiple transactions within a short duration, indicative of fraud.
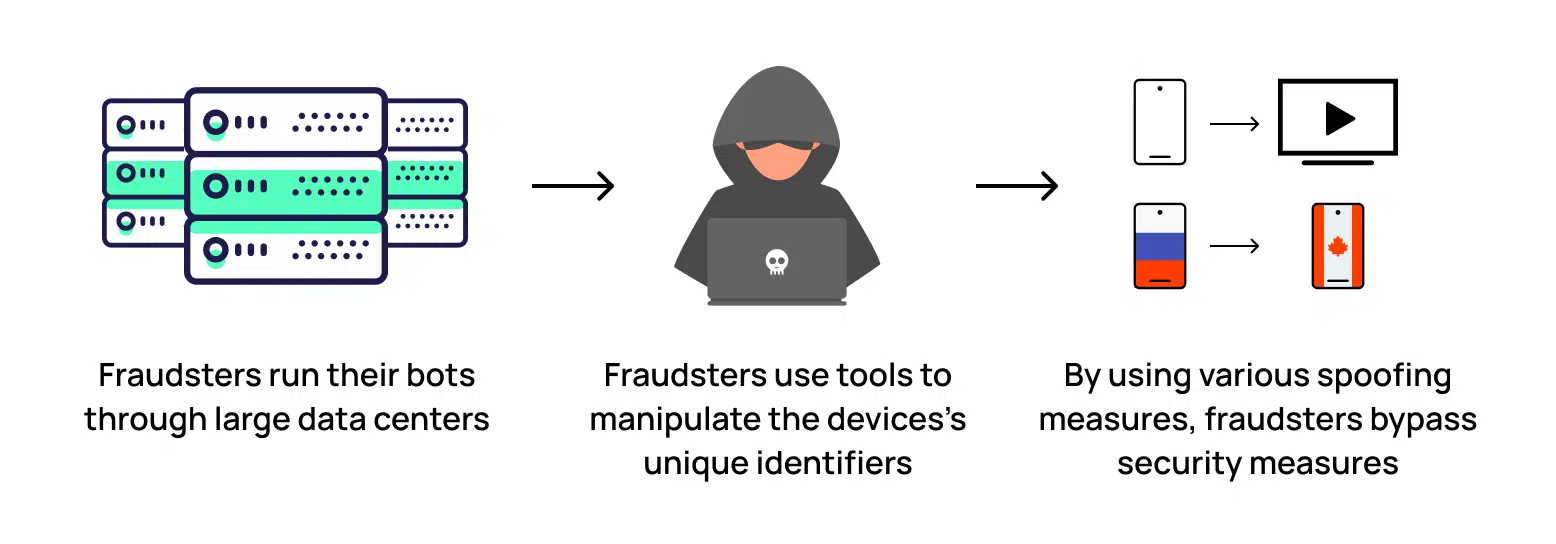
Device intelligence is becoming a popular tool for protection against a range of cyber threats such as automated bot attacks, rooted and hooked devices, app cloners, cloud phones, and spoofed websites. It helps businesses identify whether the credentials provided by a user match with the device and any unusual activity associated with the device.
Types of frauds that device intelligence can help prevent
Due to its ability to quickly identify a wide variety of cyber threats, device intelligence is becoming a popular weapon for fraud detection. It provides organizations with crucial device forensics that facilitate early detection of fraud, which allows them to take timely action and protect their business and consumer interests.
Device intelligence is known to create hurdles for the attackers and can be successfully used to identify fraud rings. It is also useful in thwarting attacks such as:
- fake account creation
- account takeovers
- device hijacking
- promo abuse
- referral abuse
- phishing
- social engineering attacks
How device intelligence works
A device intelligence solution comes into play when a user interacts with a business system, such as creating a new account. It runs in the background and does not require any user intervention. This helps prevent introduction of unnecessary friction for users and maintain a seamless user experience across digital channels.
Device intelligence follows a layered approach to fraud detection. Usually there are four steps that a device intelligence solution follows. These include collection and analysis of device attributes, identification of genuine devices, verifying the integrity of the device, and finally, evaluating the reputation of the user.
Device intelligence enables businesses to analyze a vast collection of device attributes such as device information, screen resolution, key strokes, cursor actions, operating system, network, browser, page navigation, languages, and more. However, device intelligence does not track users’ personal information, which helps maintain user privacy.
Using artificial intelligence and advanced machine learning algorithms, a device intelligence solution evaluates the aggregated digital parameters and identifies each device, uniquely. In case, there is any divergence from the standard device behavior, the solution flags it for further review and necessary action. Further, these algorithms detect and flag attempts to bypass security mechanisms, which triggers real-time intervention.
Why device intelligence is important?
Device intelligence, combined with other digital parameters, enables businesses to recognize genuine users and optimize their digital experience across digital channels. It helps optimize fraud detection capabilities aligned with unique business needs. By identifying common signatures between customers across different situations, it helps detect anomalies and identify a plethora of fraudulent activities including account takeover fraud, fake account creation, and promo abuse, among others.
Device fingerprinting is a key element in device intelligence solutions and can be easily implemented across operating systems to uniquely identify fraud rings and repeat attackers.
Technologies/techniques used in device intelligence
Device intelligence involves several technologies and techniques to offer meaningful fraud mitigation capabilities. While device fingerprinting, artificial intelligence and advanced machine learning algorithms are the key technologies, there are several other technologies that are used in device intelligence.
Big data analytics plays a crucial role in analyzing the data aggregated using artificial intelligence and extracting actionable insights. Techniques like deep learning and neural networks enable recognition of patterns and making predictions or decisions. Internet of Things (IoT) helps connect and communicate with other devices and integrate them into a network to share data, collaborate, and make intelligent decisions collectively.
Edge computing is used to process data locally on the device or at the network edge to facilitate real-time decision-making. This reduces latency, improves response time, and enhances privacy. Computer vision techniques are used to analyze visual data from images or video streams, including object recognition, image classification, object tracking, and facial recognition, among others. By overlaying the digital information onto the physical world or creating immersive virtual environments, Augmented Reality and Virtual Reality technologies enhance device intelligence. Further, use of context-awareness helps understand a user's situation, location, preferences, and other relevant factors.
Arkose Labs’ device intelligence protects against myriad fraud types
Arkose Labs uses device intelligence as an important weapon in thwarting fraud attempts without subjecting good users to the same treatment. This allows businesses to successfully fend off a myriad of cyberattacks while maintaining the superior user experience they are known for.
Device intelligence at Arkose Labs uses a blend of technologies including device fingerprinting, advanced machine learning models, and behavioral biometrics, among others, to automatically stop bot attacks and recognize human click farms and fraud farms. This unique combination of technologies enables us to get more information about attributes such as the screen, CPU, web browser, memory, and the operating system that play an important role in defining common legitimate systems.
Arkose Labs does not block any incoming user. Instead, it dynamically decides on a challenge-response authentication strategy, which is based on the extent of deviation of the session’s device signature from the ground truth. For instance, a session that deviates slightly from the defined standards is presented with a simple Arkose Matchkey challenge, whereas a significantly devious session is served a complex challenge. This targeted friction helps catch even the most impersonated bots, but without obstructing the digital journey of any good user. The volume and complexity of the challenges keeps increasing for persistent malicious users, until they are completely worn out and abandon the attack. This provides the business and its customers with long-term protection from known and evolving threats.
